Background:
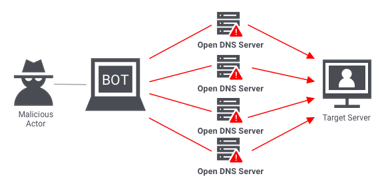
Collaborative attacks: In order to cover their tracks, sophisticated cyber actors are typically spreading out their activities in space and time, i.e., they are launching their attacks from a large number of sources where every origin is only intermittently active. This makes it difficult for defenders to spot and link these disjoint activities into an ongoing campaign and respond accordingly. To reduce the overall effort needed to develop and maintain this infrastructure, adversaries will however likely reuse (parts of) their software across these endpoints, which means that if we can spot similar software we can establish a potential link of collaboration. Software implementations often contain specific fingerprints that may be observed in the generated network traffic, and if we identify commonalities in data traffic, we can discover potential collaborators in a distributed campaign. One technique for doing so is through pairwise comparisons of network packets. If data fields are populated in a similar way using the same algorithm, a simple XOR will reveal those following the same blueprint. The technique has been demonstrated in software, but software-based implementations do not deliver the performance necessary for the high-speed and real-time requirements in practical deployments.
IP scanning: While adversaries could simply enumerate targets (for instance “counting” through IP addresses from 1.1.1.1 through 254.254.254.254), the organization of the IPv4 address space means that this behavior would be easily spotted by network owners and blocked. To limit the impact on a single network and thus hide their activities, malware often randomizes its target list. Mirai for instance uses a generator in a multiplicative group modulo a prime > 2^32, which means that all IP addresses would be hit exactly once based on a single unique seed. Knowing this internal RNG seed would predict all future activities by the malware, which enables a variety of selective defenses. Previous work has demonstrated the applicability of this approach, but the required brute-forcing of the remaining entropy combined with the limited speed of CPU-based implementations means that a seed could only be recovered retroactively.
Thesis goals: Develop mechanisms for collaboration discovery in hardware, leveraging the massively-parallelized pipeline of an FPGA platform. Use the capabilities provided by GPUs and FPGAs and apply them to the perfectly-parallelizable search for a malware’s RNG seed under real-time constraints. This will enable it to contain, redirect and tarpit malware already while the attack is in progress.
Keywords: Botnet, hardware acceleration, DDoS, Collaborative attacks, IP scanning
Prerequisites: Digital hardware design, FPGA design, hardware security
Optionally: Python, network security
Further reading:
[1] H. Griffioen and C. Doerr, “Discovering Collaboration: Unveiling Slow, Distributed Scanners based on Common Header Field Patterns,” NOMS 2020 – 2020 IEEE/IFIP Network Operations and Management Symposium, 2020, pp. 1-9, doi: 10.1109/NOMS47738.2020.9110444.
[2] Harm Griffioen and Christian Doerr. 2020. Examining Mirai’s Battle over the Internet of Things. In 2020 ACM SIGSAC Conference on Computer and Communications Security (CCS ’20)
[3] Harm Griffioen and Christian Doerr. 2020. Quantifying Autonomous System IP Churn using Attack Traffic of Botnets. In The 15th International Conference on Availability, Reliability and Security (ARES 2020)
Miscellaneous: This is a PhD position offered jointly by the Delft University of Technology (Quantum & Computer Engineering department) and the Hasso-Plattner-Institut (Cyber Threat Intelligence Lab). It offers dual working locations (Delft, Berlin), access to extended resources and a truly interdisciplinary environment for conducting research.
